Phishing is one of the biggest dangers to network security. It’s responsible for a majority of cyberattacks and continues to get more sophisticated all the time. It’s an all-purpose vehicle for everything from credential theft to ransomware injections.
In the first quarter of 2021, phishing attack volume jumped 22% from the same time the year prior. This is after we’ve already seen huge increases in volume during 2020 due to the disruption of the pandemic.
Phishing continues to be so effective because it preys upon human error. A human being is much easier to trick than an algorithm in an anti-malware application.
Training employees on how to detect phishing emails is an ongoing challenge for employers. They may hit the basics in an annual cybersecurity presentation, but those basics can be easily forgotten if not provided regularly.
One acronym that gives employees an easy way to remember phishing detection tips is SLAM.
SLAM is used to highlight the four key areas of an email that employees should check before taking any type of action on it. This pause to check those four areas also helps break the cycle of responding due to an emotional trigger, such as fear, before thoroughly evaluating an email. Emotional triggers are something attackers use to entice action immediately.
SLAM stands for:
- Sender
- Links
- Attachments
- Message
When employees are well trained in cybersecurity awareness, a company’s risk of a breach can go down as much as 70%.
Here’s how you use this tactic to train your employees and sharpen their phishing identification skills.
Check the Sender
First, you want to look at the sender’s email address in the “From” line of the email message. You have to look past any text name and evaluate the email address itself.
- Does it come from a domain you recognize? (Note: even if it passes this check, it could still be a fake)
- Does the address use a subdomain (e.g., service@subdomain.amazon.com)?
- Does the email address match the originator you see when you view the source code of the message header?
Phishing campaigns will often use a fake email address in the sender line or one that is very close to a real address, close enough to fool most users.
For example, this clever fake that looks just like a real email from Bank of America is actually using a fake address that is dressed up to look like the real thing (bankofamerica@emcom.bankofamerica.com).
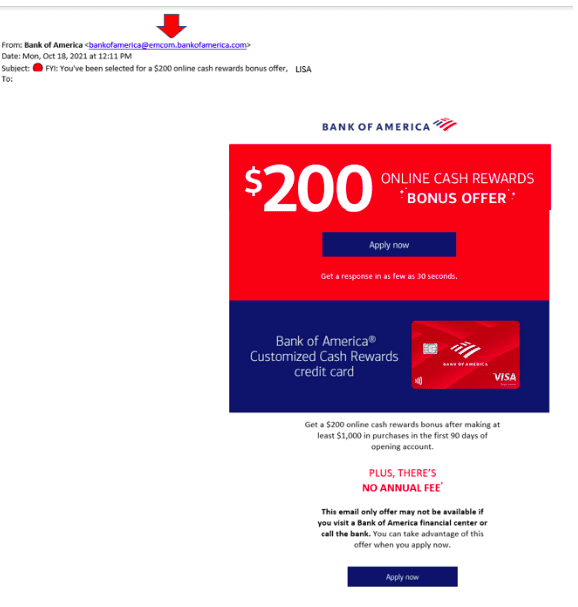
The average user would most likely think that is a legitimate address and the “emcom” part maybe has something to do with their email marketing service. But a quick Google search is all it takes to reveal this address is a scam.
Check the Links
Hyperlinks also need to be checked before they are clicked on. Even innocent-looking ones that seem to go to a shared OneDrive file, can be leading to a phishing site.
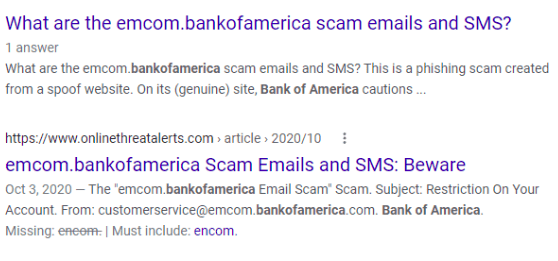
Hovering over the link on “right here” reveals that is not a real AT&T email.
Hover over links before you click them to see the real URL they are pointing to. You should also always check with colleagues if you get an email that looks to be from their email address and includes an unexpected link.
It’s best to always go directly to a website by typing its address in a browser rather than going through an email link, just in case that email is a phishing scam.
Check the Attachments
File attachments of all types can contain malware and will unleash it as soon as the attachment is opened. Even files like PDFs can use code that can launch an attack on your system.
Never open email attachments that you aren’t 100% expecting and have verified as legitimate. You should also have a reliable antivirus/anti-malware program that scans all email attachments for threats.
Check the Message
Spelling and grammar errors are giveaways that an email is not legitimate. However, these can be easy to miss if you’re just scanning the email quickly and not thoroughly reading it.
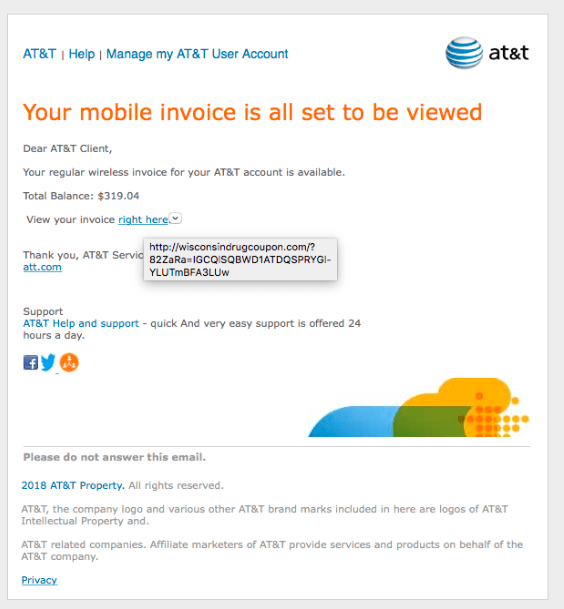
Take a look at this email below (we already see by hovering over the link that it’s a scam), but can you see the other clue that is a phishing email?
Look at the second sentence of the email. It says “We confirmation that your item has shipped” instead of we confirm. This is a grammatical error that the real Amazon would most likely not make. But it’s easy to miss if you’re not reading the message carefully and looking for errors.
Get Expert Help Training Your Team on Security Awareness
Rocky Knoll Technologies can help your Charlotte area business reduce the risk of a cyberattack by putting an ongoing employee security awareness training plan in place that sharpens phishing detection and other data security skills.
Schedule a consultation by calling 704.594.7292 or reach us online.



